| Role Availability | Read-Only | Investigator | Analyst | Manager |
About Suppression Rules
USM Anywhere includes suppression rules which enable you to manage and . After you have confirmed that these issues do not pose a security threat, create a suppression rule to prevent them from displaying in the user interface (UI), and avoid noise in your system.Warning: Orchestration rules only apply to future events and alarms.Suppression rules using the
Contains, Match and Match, case insensitive operators apply to future events and alarms, not to events and alarms received in the current day.Note: USM Anywhere saves the events that match a suppression rule, but does not correlate these suppressed events. By default, USM Anywhere hides these suppressed events. If you want to see these events, click Suppressed in the Search & Filters area. The table displays suppressed events along with all events. See To only display the suppressed events if you want to display just the suppressed events.
Note: The suppression rule you create will apply to future items. It also will apply to items of the current day, up to 10 K events/alarms.
Managing Suppression Rules
USM Anywhere enables you to manage your own suppression rules from the All Orchestration Rules page. To create a suppression rule from the orchestration rules page- Go to Settings > Rules.
-
Select Create Orchestration Rule > Suppression Rules.
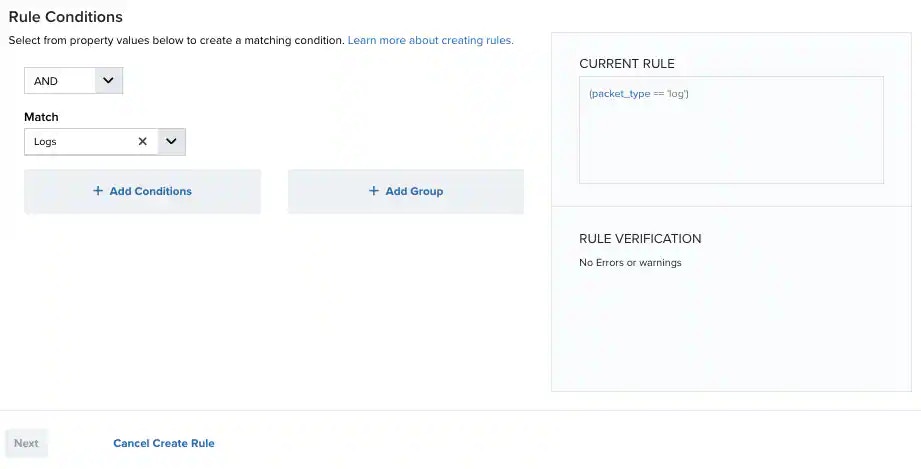
- Select a Boolean operator. The options are AND, OR, AND NOT, and OR NOT.
-
Select a packet type in the Match drop-down list.
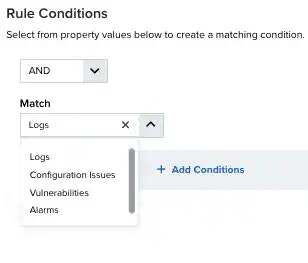
- Logs: Use this packet type for event-based rules.
- Configuration Issues: Use this packet type for configuration issues-based rules1.
- Vulnerabilities: Use this packet type for vulnerabilities-based rules.
- Alarms: Use this packet type for console user alarms-based rules.
- Click Add Conditions and select the property values you want to include in the rule to create a matching condition.
Note: If the field is related to the name of a country, you should use the country code defined by the ISO 3166.
Note: The Sources or Destinations field needs to match the universally unique identifier (UUID) of the event or alarm. You can use the Source Name or Destination Name field instead.
Note: If you need to add a property value that maps with a property key, you need to know the mapping of the field. See Determining the Mapping of a Field for more information.
-
(Optional.) Click Add Group to group your conditions.
Note: See Operators in the Orchestration Rules for more information.
-
In the Occurrences text box, enter the number of event occurrences that you want to produce a match on the conditional expression to trigger the rule.
You can enter the number of occurrences or use the arrows to scroll the value up or down. You can enter a number between 1 and 100.
Note: The current rule box shows you the syntax of your rule, and the rule verification box reviews that syntax before saving the rule.
-
Click Next.
- Enter a name for the rule.
- (Optional.) Enter a description for identifying this rule.
-
In the Length text box, specify the timespan that you want to use to identify a match for multiple occurrences. Enter the number in the text box, and then use the drop-down menu to select a value of seconds, minutes, or hours.
This duration identifies the amount of time that transpires from the beginning to the end of the occurrence. If the number of occurrences is not met within this period, the rule is not a match.
Note: Your defined length and occurrences function together to specify the number of occurrences within a time period that will produce a match for the rule. For example, you can define a rule to trigger an for an attempt when a failed occurs three times within a five-minute window.
- Click Save. The created rule displays in the list of rules. You can see it from Settings > Rules. See Orchestration Rules for more information.
- Go to Settings > Rules.
- Click the box next to Filter By.
- Enter your search.
- Go to Settings > Rules.
- Click the combo box next to Rule Status.
- Select All Rules, Enabled, or Disabled.
- Go to Settings > Rules.
- Click the
icon of the rule you want to edit.
- Modify the data of the items that need to be modified.
- Click Next.
- Click Save.
- Go to Settings > Rules.
- Click the
icon of the rule you want to delete.
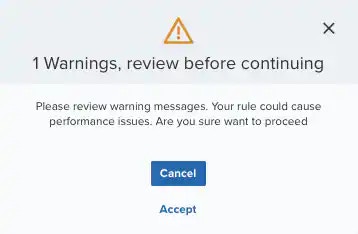
- Confirm by clicking Accept.
- Go to Settings > Rules.
- Click the
icon of the rule you want to enable.
- Go to Settings > Rules.
- Click the
icon of the rule you want to disable.
- Go to Settings > Rules.
- In the list of rules, select the first checkbox in the first column to select all the rules.
- Click Enable All Rules.
- Go to Settings > Rules.
- In the list of rules, select the first checkbox in the first column to select all the rules.
- Click Disable All Rules.
- Confirm by clicking Accept.